There is a elementary query you’ll be able to ask of each the web and actual life: “How do I take pleasure in my time right here with out taking pointless dangers?” In grass-touching meatspace, you’ll be able to reduce out processed meals, carry pepper spray and keep away from skydiving with out a accomplice.
However the greatest strategies for staying protected on-line aren’t as intuitive. The web is an enormous city sq. the place folks are always bellowing deeply private info about themselves. It is no shock that it is grow to be a breeding floor for scams, theft and different prison exercise.
Given the breadth of risks, it could really feel simpler to throw up your fingers and say that no matter occurs will occur. I am right here to inform you, although, that cybersecurity does not have to be complicated, troublesome or time-consuming. You do not want to be a hacker to foil a hacker — you solely have to reap the benefits of easy suggestions and free apps designed to make you safer on-line. Whether or not you commit to all 12 detailed right here or solely focus on one, you will be way more safe for it.
1. Set up safety updates instantly
One in every of the most essential issues you are able to do to guarantee your digital safety is to set up all software program updates as quickly as they grow to be out there on your units. If you see the notification, do not wait — prepare your self to obtain the replace instantly.
Not all software program updates are about safety, however the ones that are kind your greatest line of protection in opposition to technical hacks. When builders uncover a flaw that may be exploited, they ship an replace to repair it. By the time the flaw will get patched, possibilities are very excessive that hackers additionally find out about it, so any time misplaced means you possibly can be the subsequent to get exploited.
As you go down this record, you will study that cybersecurity threats are much less technical than you assume. To counter the ones that are, nonetheless, there’s nothing extra essential you are able to do than set up safety updates.
2. Use sturdy passwords
Weak, simply guessed passwords are one in all the most frequent causes of information breaches and malware assaults. If a password is one in all the ten or so commonest, an attacker could give you the chance to guess it with no different information. If it is linked to you — your birthday, say, or mom’s maiden identify — it could be guessable from information anybody can lookup on-line.
Even when your password is a random string of characters, it’d nonetheless be guessable if it is too brief. Hackers can use applications to guess all potential mixtures and check out every one on a goal account. The longer a password is, the extra exponentially troublesome it is to guess.
SEAN GLADWELL through Getty Photographs
Meaning you want passwords that are each lengthy and meaningless to you. You would possibly rightly complain that these are bastards to keep in mind, however you are in luck: password managers can try this for you. A password manager app or browser extension can create passwords whenever you want them, retailer them securely and fill them in mechanically. All you’ve got to keep in mind is the one grasp password that unlocks all the others.
3. Arrange two-factor authentication
Even the strongest password would possibly get revealed by no fault of your personal, like if it is saved with out encryption and leaked in a knowledge breach. That is why it helps to have two-factor authentication (2FA), also called multi-factor authentication (MFA), as a second safe layer on each account.
You in all probability already know 2FA as the irritating further step that makes you go get your cellphone — however that is not the solely method to do it. Many apps, together with Google and Apple, now allow you to log in by passkeys. These not solely do not require you to enter a code or password, however use uneven encryption, sharing credentials between your gadget and the service that runs the passkeys. It is rather a lot faster for you, and leaves nothing to steal.
4. Again the whole lot up
Ransomware and its cousins are a progress business inside the cybercrime financial system. These assaults corrupt your recordsdata or lock you out of them till you pay a payment to get them again. The best method to foil a ransomware assault, or to clear some other sort of malware off a tool, is to restore the complete system from the most up-to-date backup.
To ensure you even have a backup, consultants advocate the 3-2-1 rule: three completely different backups, on two various kinds of storage, with not less than one bodily distant from the principal system. For instance, you possibly can have one backup on one other gadget in your own home, one in the cloud and one on a transportable laborious drive. Computerized backup providers can save disk photos for you at set intervals so you do not have to keep in mind to do it your self.
5. Study to spot social engineering
Regardless of all the technobabble flying round the cybersecurity world, an excellent many scams and hacks are achieved by strategies a Nineteenth-century con artist would acknowledge. Scammers pose as consultants or authority figures to acquire your belief, and use horrifying language to bypass your crucial pondering. Ticking clocks, emotional manipulation and faux identities are all in the toolbox.

Alex Cristi through Getty Photographs
Take phishing, through which hackers trick you into giving up your information willingly. A typical phishing electronic mail would possibly pose as a financial institution, credit score bureau or different authoritative service. In crimson letters, it could demand your financial institution password or social safety quantity to instantly repair an irregularity along with your account. Different frequent approaches embody warning you about rushing tickets you by no means incurred or sending receipts for subscriptions you by no means purchased.
Social engineering assaults are always evolving, however they usually fall again on the identical methods. One of the best ways to foil them is to take a deep breath each time you obtain a daunting electronic mail or textual content message, then analysis it intimately: lookup the electronic mail handle, verify the visible design to ensure the sender is who they declare to be, and ask your self if there’s any method the message may very well be true. I extremely advocate working by this phishing quiz — it is robust, however honest, and very academic.
6. All the time verify hyperlinks before clicking
This is a companion to the earlier tip. Social engineering scams do not at all times attempt to get you to quit information your self. Additionally they get you to click on on hyperlinks that put secret malware on your gadget — like keyloggers that watch you kind your passwords or ransomware applications that corrupt your recordsdata.
In the event you’re ever not certain about an electronic mail attachment or a hyperlink you are being requested to click on, copy the hyperlink (with out opening it) and paste it right into a URL checker like this one from NordVPN. These free instruments can inform you if a hyperlink is related to any recognized malware domains.
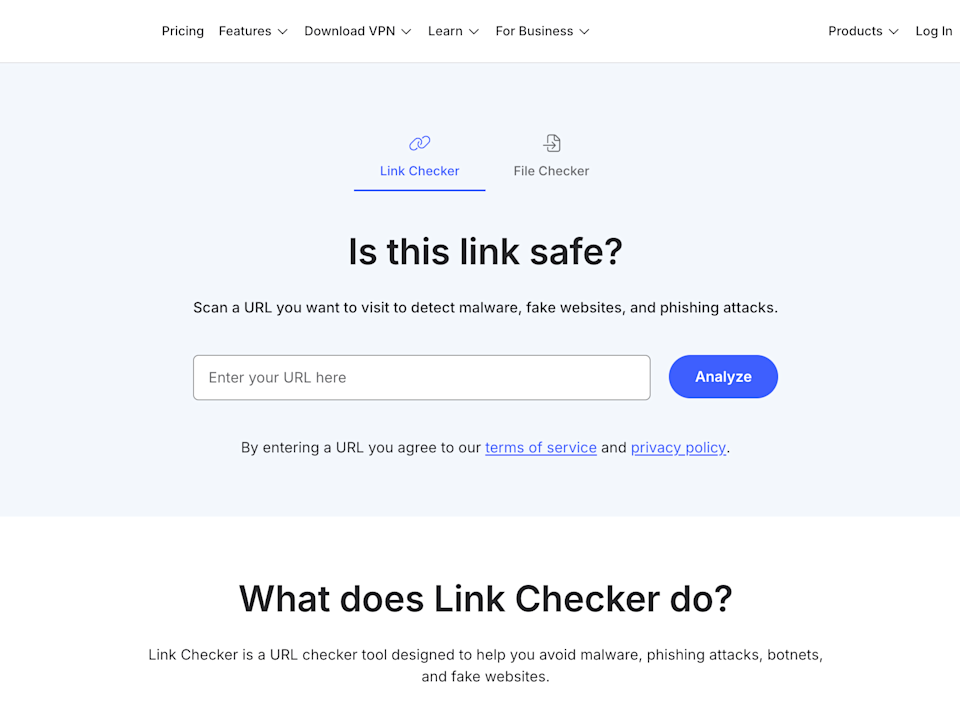
Sam Chapman for Engadget
It’s also possible to mouse over any hyperlink, then take a look at the bottom-left of your browser to see what URL it is going to take you to. If an electronic mail is from your financial institution, any hyperlinks inside it ought to go to your financial institution’s web site. If it is going wherever else, particularly to an unidentifiable string of characters, be suspicious.
7. Do not overshare
Over the final twenty years, a number of us have gotten into the behavior of dumping all types of private information on social media. This development has supercharged the rip-off financial system. It might appear innocent to broadcast the names of your children or the dates you will be on trip, however every bit of information you set into the world makes it simpler for a stranger to get hooks into you.
For instance, “grandparent scams” are on the rise proper now. Grifters contact a goal, often a senior, pretending to be their grandchild. They’re going to declare to be in a disaster and wish cash quick. The extra information they’ve on their goal, the extra convincing their story of woe shall be. Social media is a chief place to research a possible sufferer.
Oversharing may also be a compounding drawback. In the event you use weak passwords, your public information can be utilized to guess your credentials or reply your safety questions. So, if you do not have a password supervisor but, assume twice before you have interaction with that quiz publish on Fb that asks for the identify of your childhood pet.
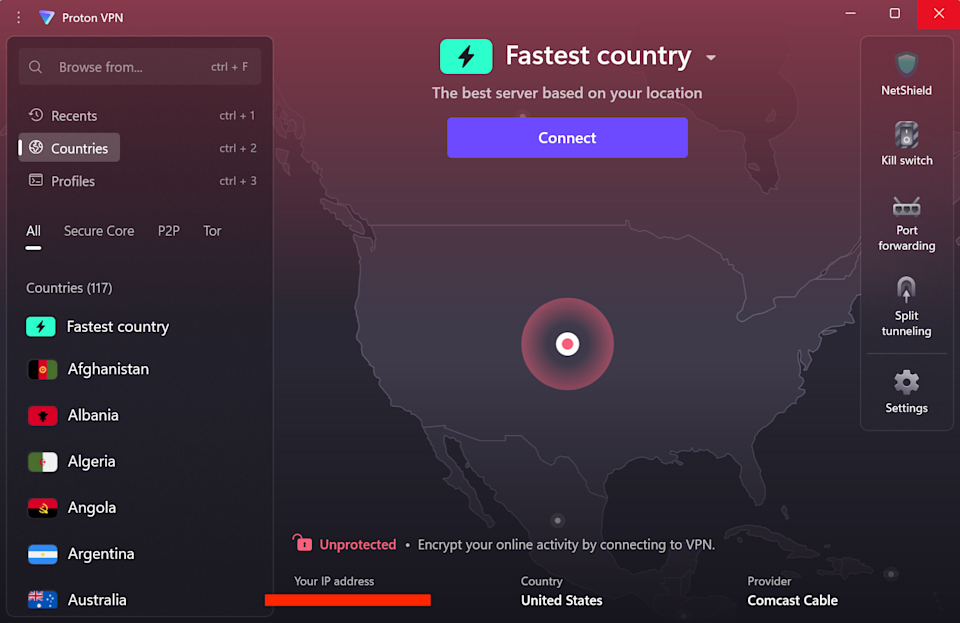
8. Use a VPN
I am an enormous booster of digital personal networks (VPNs), nevertheless it’s essential to be practical about what they will and might’t do. Even the best VPNs aren’t whole cybersecurity options — you’ll be able to’t simply set one and assume you are protected eternally. A VPN cannot shield you if you happen to use simply guessed passwords, for instance, or click on on a malware hyperlink. It is about hiding your identification, not making you invulnerable.
So what can a VPN do? Briefly, it replaces your IP handle (a fingerprint that identifies you on-line) with one other IP handle, belonging to a server owned by the VPN. The VPN server does enterprise with the web on your behalf, whereas its conversations along with your gadget are encrypted so it may’t be traced again to you.
Sam Chapman for Engadget
This means no third social gathering can join your on-line actions along with your real-world identification. No one shall be harvesting knowledge on the web sites you go to to promote to advertisers, nor constructing a file on you that an unscrupulous authorities would possibly misuse. VPNs additionally shield you from pretend public Wi-Fi networks arrange by cybercriminals — even when a hacker tips you with a man-in-the-middle assault, they can not do a lot with out your actual IP handle.
Many high VPNs, together with my high choose Proton VPN, embody advert blockers that may additionally maintain cookies and monitoring pixels from latching onto you. So, even when a VPN cannot do the whole lot, you will be far safer and extra personal with one than with out one. In the event you don’t need to pay for a brand new subscription proper now, I’ve additionally compiled a listing of the best free VPNs that are really protected to use.
9. Run common virus scans
A very powerful time to search for malware is whenever you’re downloading a file from the web. Not solely can undesirable apps hitch rides on seemingly protected recordsdata, however hyperlinks can begin downloads in secret, even if you happen to do not assume they’re meant to be downloading something. A stable antivirus program can catch malware because it arrives on your system, and if it is unsure, can lock suspicious recordsdata in quarantine till it is aware of whether or not they’re protected or not.
Devoted antivirus apps are generally even able to catching malware that hasn’t been seen or used but. AV software program makes use of machine studying to establish the frequent patterns of malware, filtering out new viruses that behave like outdated ones.
However what about malware that is already gotten by the perimeter? An antivirus app also can verify your pc at set intervals looking for undesirable apps, together with people who is perhaps masquerading as system recordsdata. Home windows computer systems now come pre-installed with Home windows Defender, which is sufficient to deal with most of those duties, however I like to recommend not less than one anti-malware program on any gadget.
10. Use electronic mail maskers and personal serps
In the event you’re involved about your information being misused or mishandled, do not forget that the much less you set out into the world, the much less hazard you are in. Preserving your personal knowledge off social media is one essential step, however there are different methods your knowledge will get disseminated — and different choices for responding.
For instance, you usually want an electronic mail handle to join a web-based account. In the event you use your actual electronic mail, your contact information is now floating round on-line, rising the likelihood of somebody utilizing it to rip-off you (or not less than including you to mailing lists you by no means signed up for). To remain protected, use an electronic mail masker. These providers offer you a pretend electronic mail handle you should use to create accounts, which mechanically forwards messages to your actual handle.
Sam Chapman for Engadget
Search engines like google, particularly Google, are additionally infamous for constructing profiles on customers by watching the phrases they seek for. You possibly can dodge that by switching to a personal search engine like DuckDuckGo, which does not observe something you do — it is funded by non-targeted advert gross sales on its search outcomes pages, not by promoting your knowledge to brokers.
11. Use a knowledge removing service
Talking of information brokers: sadly, if you happen to’ve been on the web at any level in the final 10 years with out taking intense precautions, your knowledge is in all probability in the fingers of not less than one enterprise that makes cash by hoarding and promoting it. These knowledge brokers vary from public-facing, people-search websites to personal backend sellers.
Knowledge brokers are poorly regulated and lax about security. The longer one has your private information, the extra possible it is to leak. The excellent news is that the majority brokers (although not all of them) are legally required to delete your knowledge if you happen to ask them to.
Nonetheless, there are a whole lot of knowledge brokers on the market, they usually actually need to maintain your knowledge. Every one makes opting out more durable than uninstalling a Norton product — and tons of of them could have recordsdata on you. To make the course of simpler, you should use a knowledge removing service like DeleteMe or Surfshark VPN’s accomplice service Incogni.
12. Apply bodily safety
Let’s shut out the record by getting a little bit old-fashioned. I’ve already mentioned what number of on-line scams rely on traditional con artistry to work. By the identical token, bodily infiltration and smash-and-grab techniques nonetheless pose a menace to cybersecurity.
It does not take an excessive amount of creativeness to see how this might work. In the event you depart your laptop computer or cellphone unattended in public, for instance, somebody would possibly insert a flash drive that masses malware onto the system. In a single illustrative case, a thief in the Minneapolis area would loiter in bars, watch folks unlock their telephones, then steal these telephones and unlock them himself.
I am not saying you want to be paranoid each second you are in public. Simply use the identical stage of warning you’d use to shield your automotive. Lock your cellphone with a biometric key so solely you’ll be able to open it, and ensure not to depart any gadget mendacity round if it may entry your on-line accounts. And at work, watch out not to let anybody right into a safe space if they do not have the correct credentials.
Disclaimer: This article is sourced from external platforms. OverBeta has not independently verified the information. Readers are advised to verify details before relying on them.